The majority of organizations assume that the work is complete once they survive a cyberattack. They re-establish the systems, regain access, and resume operations. This brings a large problem, though. Unless you ever go out to determine how exactly the attack occurred, you remain vulnerable to the same threats.
This is where digital forensics comes in.
Containment halts the immediate harm. Digital forensics explains what took place. It answers the important questions: how the attacker got in, what areas they reached, how long they remained inside, and if they have actually left. Without those answers, organizations base decisions on guesswork rather than solid information.
A professional Digital Forensics company goes beyond basic checks. It rebuilds the full sequence of events. It creates a detailed timeline, identifies security gaps, and provides evidence-based findings to prevent future attacks. Digital Forensics services have become necessary. They form a core part of cybersecurity for any serious organization.
Why Identifying Root Cause Is Critical After a Cyber Attack
Stopping an attack counts as only the opening move. The true benefit comes from learning its source. Without root cause analysis, organizations leave themselves open to the exact weakness that attackers used before.
The Risk of Superficial Recovery
Many organizations put all their effort into bringing systems back online fast. This gets business moving, yet it leaves the real problem untouched. Attackers frequently plant ways to stay inside, so they can come back whenever they want. Without a forensic check, these hidden risks stay unnoticed.
Repeated Attacks from the Same Entry Point
If the first access method stays unknown and unfixed, attackers skip the work of finding fresh ways in. They just use the same opening again. This explains why many organizations suffer new breaches soon after they recover. Digital Forensics services make sure the original weakness gets found and sealed for good.
Compliance and Legal Exposure
Rules and regulations demand that organizations know and report the details of any breach. Without forensic proof, meeting those requirements becomes difficult. A reliable Digital Forensics company makes certain that the work follows legal rules and produces evidence that stands up when needed.
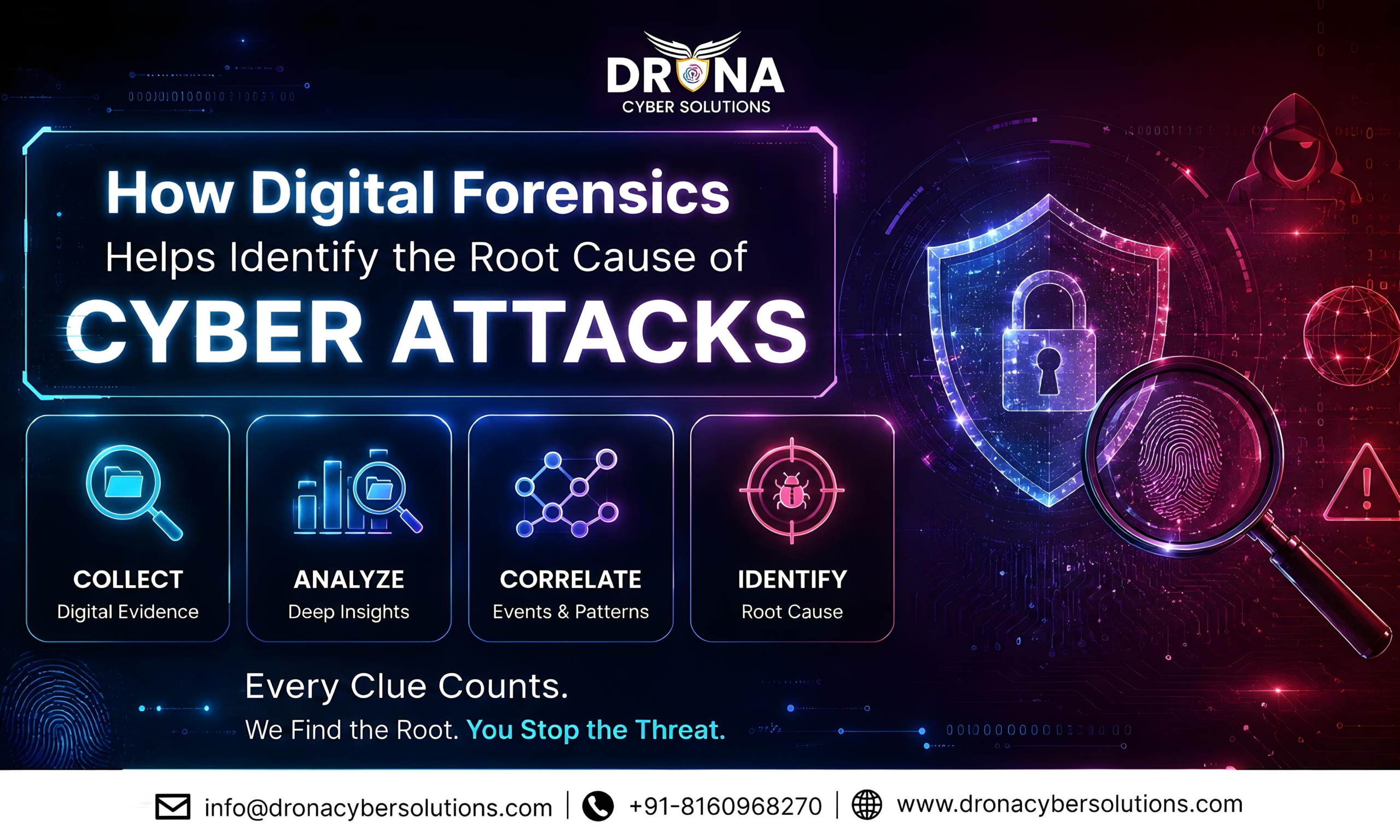
How Digital Forensics Identifies the Root Cause
Digital forensics avoids guesses. It creates a clear reconstruction of the attack from collected data and records.
Tracing the Initial Entry Point
The opening task in every forensic review involves finding how the attacker first broke in. This might happen through phishing emails, unpatched software, stolen login details, or badly set up systems. Experts review logs, messages, and entry records to locate the precise access route.
Reconstructing the Attack Timeline
After confirming entry, investigators build the full sequence of actions. They follow every move the attacker made, starting from the first breach through movement across systems and any data removal. This sequence shows exactly how the attack developed and which defenses broke down.
Identifying Compromised Assets
Digital forensics shows which systems, user accounts, and information got touched. This prevents organizations from missing affected parts during cleanup. It also guides teams on which fixes matter most based on the actual damage.
Detecting Persistence Mechanisms
Attackers seldom exit after their first steps. They set up ways to keep control over time. Forensic review uncovers backdoors, planned tasks, or extra accounts created for return access. Clearing these out proves necessary for full recovery.
Understanding Data Exposure
One key result from digital forensics is learning exactly which data attackers viewed or took. This detail supports required reports, talks with customers, and proper evaluation of the risks.
Role of Digital Forensics in Incident Response
Digital forensics does not work on its own. It forms a central piece of the overall incident response effort.
Supporting Faster and Accurate Decisions
When an incident is underway, teams need to act without delay. Forensic details supply clear facts that guide the best choices. Without this information, teams depend on guesses that can cause wrong moves.
Enhancing Containment Strategies
Forensic work reveals how widely the attack reached. This lets teams limit the problem more precisely and avoid shutting down systems that remain clean.
Strengthening Recovery Processes
Recovery involves more than reloading systems. It requires confirming the whole setup stays protected. Digital forensics checks that every threat has been cleared before operations restart.
Common Mistakes Without Digital Forensics
Organizations that avoid forensic work usually deal with lasting problems.
Assuming the Threat Is Fully Removed
Without a thorough review, organizations often think the danger has ended when pieces of it still exist. Undetected backdoors and altered accounts can stay active.
Ignoring Evidence Preservation
Skipping proper evidence handling makes it hard or impossible to learn the full story. This also creates serious issues during legal or compliance reviews.
Relying Only on IT Teams
IT staff handle vital tasks, but digital forensics calls for specific skills and tools. A professional Digital Forensics company supplies the right methods and background for proper results.
How to Choose the Right Digital Forensics Company
Different providers offer different skill levels. Picking the correct one has a direct effect on investigation quality.
Experience in Handling Real Incidents
A strong provider needs proven work on actual cyber events in many sectors. This prepares them for difficult cases.
Advanced Tools and Methodologies
Digital forensics depends on purpose-built tools for gathering and studying data. The best providers apply current technologies that deliver precise and efficient results.
Compliance and Legal Readiness
All investigation steps must satisfy legal and regulatory demands. A solid Digital Forensics company keeps every process properly documented and compliant with rules.
Why Drona Cyber Solutions Is the Right Choice
Picking the right partner for digital forensics goes past technical skills alone. It centers on trust, precision, and quick action.
Drona Cyber Solutions stands as a top Digital Forensics company focused on accurately identifying the exact source of cyber events. Our Digital Forensics services provide a comprehensive picture of attacks, covering every stage from entry to full impact.
We join strong forensic tools with skilled review to produce straightforward, useful findings. Our method protects evidence, meets compliance requirements, and accelerates safe recovery. From ransomware cases to data leaks and insider issues, we help organizations learn the full story and prevent future repeats.
Conclusion
Cyber incidents do not finish when systems come back online. They finish once the root cause gets fully known and removed.
Digital forensics supplies that clear view. It turns unknowns into proven facts, assumptions into solid details, and basic recovery into lasting protection. Organizations that use Digital Forensics services do more than react to attacks. They build stronger defenses overall.
Without forensic work, every recovery stays short-term. With it, each incident turns into useful knowledge that improves the organization.
Drona Cyber Solutions makes sure your organization avoids open questions. We provide detailed, evidence-based reviews that reveal the reality of every cyber event and let you move ahead with certainty and full oversight.